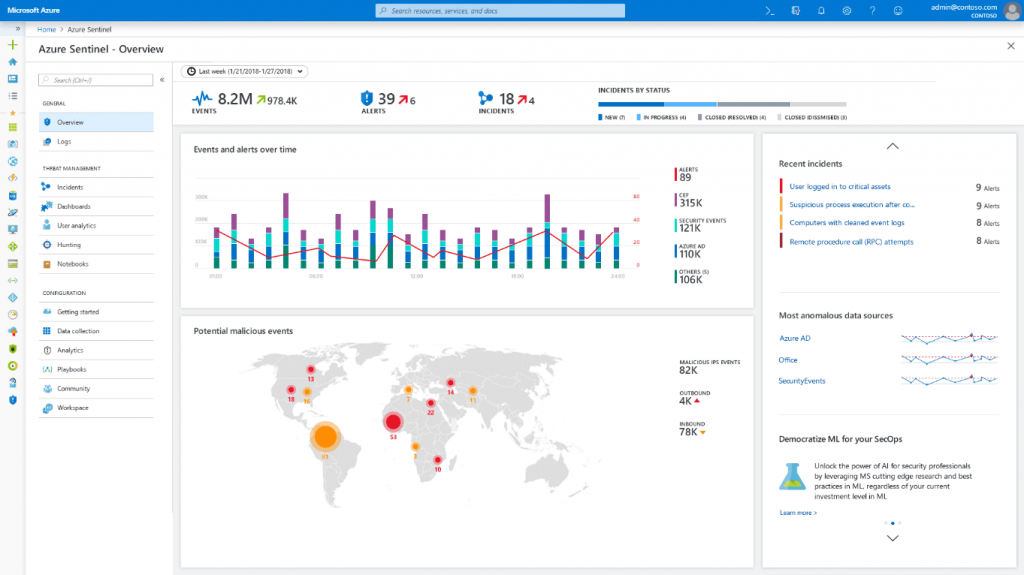
Security Information and Event Management (SIEM) can be an incredibly useful tool for safeguarding businesses of all sizes and IT systems. Azure Sentinel, a Microsoft SIEM solution, provides intelligent security analytics at the cloud scale for your entire enterprise. Here are some of the ways how Azure Sentinel makes threat protection smarter and faster.
Data Aggregation
SIEMs gathers security event information from the entire network, centralizing the data collection in a single-pane-of-glass. Azure Sentinel makes it easy to collect security data across your entire hybrid organization from devices, to users, to apps, to servers on any cloud. It uses the power of artificial intelligence to ensure you are identifying real threats quickly and unleashes you from the burden of traditional SIEMs by eliminating the need to spend time on setting up, maintaining, and scaling infrastructure. Since it is built on Azure, it offers nearly limitless cloud scale and speed to address your security needs.
Data Normalization
SIEM solutions not only collect data; they normalize it. In other words, they reformat the data in whatever format you desire, not only allowing for consistency in your log management but for easy correlation.
Azure Sentinel uses Azure Monitor, which is built on a proven and scalable log analytics database that ingests more than 10 petabytes every day and provides a very fast query engine that can sort through millions of records in seconds.
Compliance
SIEM helps enterprises patch their IT environments and helps to regulate third-party access. Both could represent security holes and compliance failures if not properly secured. Azure Sentinel has great integration capabilities too because it connects to popular solutions like Palo Alto Networks, F5, Symantec, Fortinet, and Check Point with many more to come.
Threat Detection and Security Alerting
When your solution detects a correlated security event, it can send your IT security team an alert prompting an investigation. This allows your team to focus their efforts on specific potential problem areas and discern whether your enterprise suffered a breach. From there, they can run your incident response plan and remediate the threat as quickly as possible, reducing the damage you suffer.
Filters the noise – Azure Sentinel uses state of the art, scalable machine learning algorithms to correlate millions of low fidelity anomalies to present a few high fidelity security incidents to the analyst.
Optimized Dashboards – Azure Sentinel integrates with Microsoft Graph Security API, enabling you to import your own threat intelligence feeds and customizing threat detection and alert rules. There are custom dashboards that give you a view optimized for your specific use-case.
Automate common tasks and threat response – you want to automate response to these issues. Azure Sentinel provides built-in automation and orchestration with pre-defined or custom playbooks to solve repetitive tasks and to respond to threats quickly.
By using Azure Sentinel, you can:
- Collect data at cloud scale—across all users, devices, applications, and infrastructure, both on-premises and in multiple clouds
- Detect previously uncovered threats and minimize false positives using analytics and unparalleled threat intelligence from Microsoft
- Investigate threats with AI and hunt suspicious activities at scale, tapping into decades of cybersecurity work at Microsoft
- Respond to incidents rapidly with built-in orchestration and automation of common tasks